Cloud identity management is essentially the master key system for your entire digital operation. It's the security framework that makes sure the right people get into the right cloud resources at exactly the right time. Without a solid strategy, you’re basically leaving your digital doors wide open.
Why Cloud Identity Management Is Your Digital Gatekeeper

Think of your cloud environment as a secure, modern office building. To get inside, employees don't just get a master key; they get a specific keycard. That card only grants them access to the floors and rooms they actually need for their job.
A developer might be able to get into the server room, and an accountant can access the finance department's files. But neither can just wander into the other's workspace without explicit authorization. That’s the core idea of cloud identity management.
It’s the system that defines and manages who gets access to what in your cloud. It acts as a digital gatekeeper, checking every single access request to confirm it’s legitimate and aligns with your company's security rules. This is how you stop unauthorized users from getting anywhere near sensitive data or critical infrastructure.
More Than Just Security
But a strong identity strategy does more than just prevent breaches. It’s also critical for controlling your costs. In sprawling environments like AWS and Azure, unmanaged resources can burn through your budget in no time.
For example, a developer might spin up a powerful server for a short-term project and simply forget to turn it off. That server could run for weeks, silently racking up huge costs. This is the kind of operational chaos that effective identity management is built to prevent.
It turns your cloud operations from a potential liability into a secure, tightly managed asset. The market reflects this shift, with global spending on cloud identity solutions projected to hit $13.6 billion by 2026, according to recent industry analysis. This massive investment underscores how critical it is for businesses to secure their distributed teams and complex cloud setups.
By getting identity management right, you build a foundation that protects your valuable data while also keeping your operational expenses in check. It ensures your cloud isn't just secure, but also optimized for both performance and cost.
The Building Blocks of Modern Cloud IAM
If you want to build a solid cloud identity management strategy, you first need to get a handle on its core components. These aren't just separate tools you can pick and choose from; they're interconnected building blocks that have to work together to create a system that's both secure and efficient.
Think of it like putting together a high-tech security team for your digital assets. You'll need a gatekeeper to check IDs, a system to issue and manage keycards, and clear rules for when employees join or leave. In the cloud, these jobs are handled by a few key components that form the foundation of modern Identity and Access Management (IAM).
The Central Control Panel: Identity and Access Management
At the very heart of this system is Identity and Access Management (IAM) itself. This is your central control panel where you define who gets in and what they can do once they're there. IAM is responsible for creating and managing the digital identity for every single user and service that needs to touch your cloud resources.
It’s the definitive source that answers basic but critical questions like, "Who is this person?" and "What are they allowed to access?" Without a proper IAM framework, trying to manage access is just a chaotic and insecure free-for-all.
Key Components for a Secure Foundation
Beyond the main IAM system, several other pieces work together to lock down your environment. These add powerful layers of security while also making day-to-day operations much smoother.
- Single Sign-On (SSO): This is a huge win for both user convenience and security. SSO lets your team log in just once with a single password to get into all their different apps. This gets rid of password fatigue and cuts down on the risk of people using weak or recycled passwords. You can learn more about how an SSO identity provider works in our detailed guide.
- Multi-Factor Authentication (MFA): Today, MFA is simply non-negotiable. It forces users to prove their identity with two or more pieces of evidence, like a password plus a code from their phone. This creates a massive barrier against attackers, even if they manage to steal a password.
- Federation: This component is all about connecting identity systems across different organizations or even different clouds, like AWS and Azure. Federation allows a user's identity in one system to be trusted by another, which lets them access resources across platforms without you having to create and manage duplicate accounts.
- Lifecycle Management: This is what automates the entire user access journey, from start to finish. It handles everything from automatically giving new hires the access they need on day one to instantly revoking all permissions the moment an employee leaves. Lifecycle management makes sure access rights are always correct and up to date.
The industry is clearly moving toward these kinds of agile solutions. Cloud-based deployments now make up 42% of the total IAM market share, leaving older on-premises solutions behind. This trend underscores just how important flexible, scalable controls are, especially in hybrid environments. Understanding these core components, along with related concepts like Identity and Governance Administration (IGA), is the first step to building a truly resilient cloud IAM system.
Mastering Access with Roles and Policies
Once you’ve got a handle on the basic pieces of cloud identity, it’s time to set the rules of the road for your environment. This is where Role Based Access Control (RBAC) comes in. Instead of giving everyone the keys to the kingdom, RBAC lets you assign specific, limited permissions based on what someone actually does for their job.
Think of it like running a restaurant. The chef gets full access to the kitchen but can’t touch the cash register. A server can use the point-of-sale system to take orders but isn't allowed to wander into the kitchen. Each role has exactly the access it needs to get the job done and nothing more.
This is the Principle of Least Privilege in action. It’s a core security idea: a user should only have the bare minimum permissions needed to do their work. Using RBAC to enforce this principle is one of the most powerful moves you can make in your cloud security strategy.
Defining Roles for Your Team
To make this work, you have to define roles that actually match what your team does. This helps everyone work efficiently without opening up security holes or creating chances for expensive mistakes.
- Developers: Need to spin up and manage servers in development or testing environments. They should never have the ability to touch production systems or sensitive customer data.
- Financial Analysts: Require access to billing dashboards and cost reports to keep an eye on spending. They have no need to get into the underlying infrastructure or deployment pipelines.
- DevOps Engineers: Need broader permissions to manage infrastructure, deploy code, and monitor everything. But even their access should be audited regularly to stop "permission creep."
This kind of structured access prevents those all-too-common horror stories, like a junior developer accidentally wiping out a production database. It also helps control cloud costs by restricting who can spin up or change pricey resources. For a complete security posture, it's also smart to apply similar principles to your office network by considering best practices for identity-based access.
This diagram shows how the core components, IAM, MFA, and SSO, fit together to create a solid security foundation.
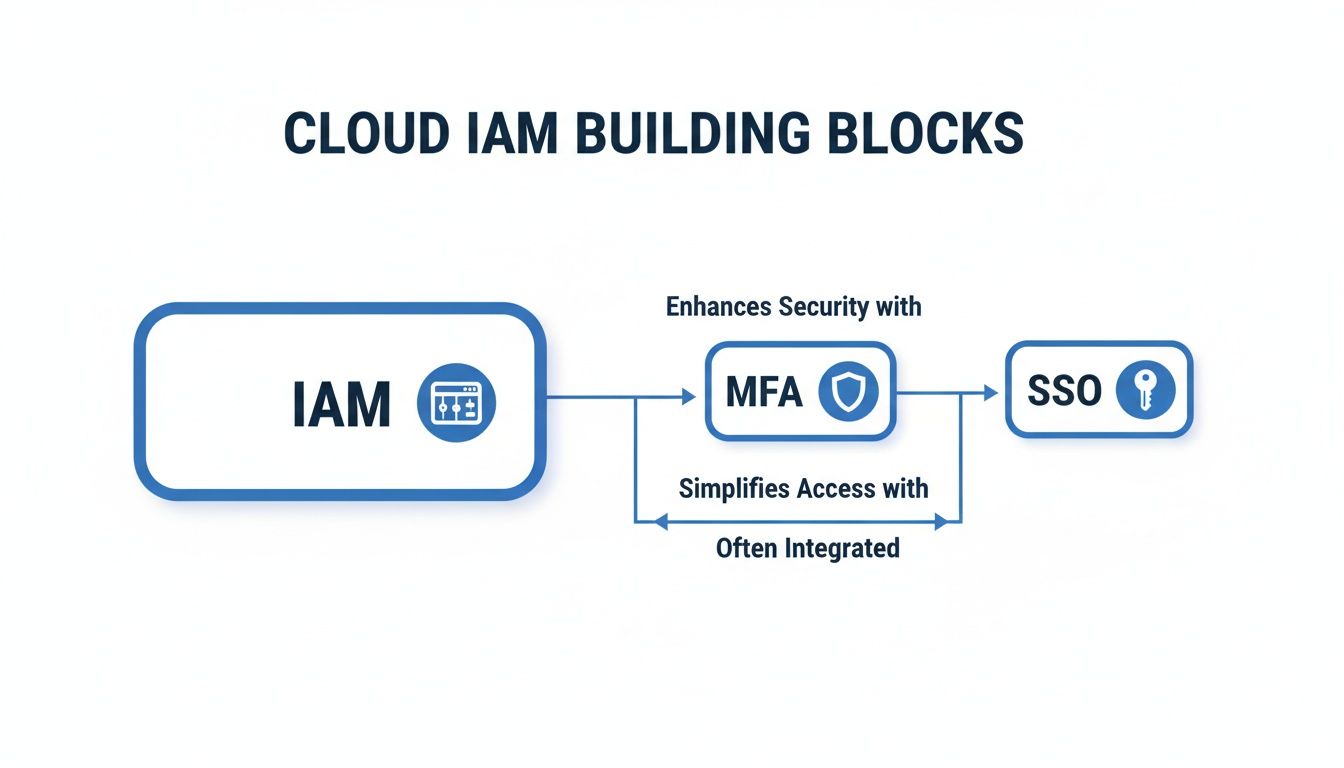
As you can see, a strong identity framework isn’t about just one tool. It’s about how multiple layers of security work together to protect your environment.
Delegating Control Without Risk
Modern tools take RBAC way beyond just who can log into the cloud console. You can delegate very specific tasks, like managing a server’s on/off schedule, without giving away broad, risky permissions. For example, a tool like CLOUD TOGGLE uses RBAC to let team members override a schedule for a critical task, but only for the specific resources they’re assigned to.
This level of detailed control is becoming standard. North America currently holds a 33.7% share of the cloud IAM market, a position it's expected to maintain through 2030. This market maturity is driving these seamless integrations, which are critical when you consider that 70% of cloud waste is tied to unmanaged access.
You can learn more about the specifics of setting this up in our guide on Role Based Access Control best practices. This approach empowers your team to help with cost savings safely, tightening security while directly helping your bottom line. You can find more details about this trend and its impact by reviewing the full industry report.
Navigating Critical Security Risks and Compliance
If you're not actively managing who has access to your cloud, you're leaving the door wide open for some serious trouble. Getting a handle on these risks is the first step to building a security strategy that actually works. The most common mistakes often create quiet, but devastating, holes in your cloud environment.
One of the biggest dangers is over-provisioned permissions. This is what happens when users get far more access than they actually need to do their jobs. Think of it as giving every single employee a master key to the entire office building. It massively increases the potential damage if just one of those "keys" or user accounts gets compromised.
Another major security hole is orphaned accounts. When an employee leaves the company, their access credentials must be revoked on the same day. If you leave them active, these accounts become a goldmine for attackers, giving them a direct and often undetected way right into your systems. A solid cloud identity management system automates this de-provisioning process so nothing gets missed.
The Real World Consequences of Poor Identity Governance
These security gaps don't just exist on paper; they lead to real, expensive problems. Weak or stolen credentials, for example, are one of the top causes of data breaches. An attacker with what looks like a valid login can waltz right through your network, grabbing sensitive customer data, intellectual property, or financial records.
The impact goes beyond just data theft. Forgotten, over-provisioned accounts often have permissions to spin up expensive cloud resources. A single high-powered server left running by a former developer can lead to jaw-dropping cloud bills, hitting your bottom line directly.
Getting these issues under control isn't just a security "nice-to-have" it's a business necessity. On top of that, many organizations have to navigate a complex web of regulatory requirements, and identity management is at the heart of meeting them.
- General Data Protection Regulation (GDPR): Demands strict controls over who can access the personal data of EU citizens.
- SOC 2 (Service Organization Control 2): Audits your company's controls over security, availability, and confidentiality, all of which hinge on strong identity verification.
- HIPAA (Health Insurance Portability and Accountability Act): Enforces rigid access controls to safeguard sensitive patient health information.
Failing to meet these standards can lead to huge fines, messy legal battles, and a damaged reputation that’s hard to repair. A proactive identity strategy is simply non-negotiable in today's regulatory environment. You can dig deeper into the various security challenges in cloud computing in our related article.
Actionable Best Practices for Your Cloud Environment

Knowing the theory is great, but putting it into practice is what actually keeps your cloud environment safe. For busy teams, that means having a clear, no-nonsense checklist. These best practices are your roadmap to a strong identity strategy that protects both your resources and your budget.
Your first and most important rule should be the Principle of Least Privilege. This isn't just a friendly suggestion; it needs to be the default setting for every user and service account. Simply put, no one gets more access than they absolutely need to do their job.
This means you have to stop using root or global admin accounts for day-to-day work. Instead, get into the habit of creating specific IAM roles with tightly focused permissions for every function, whether it's for a developer or someone in finance. Granular control needs to become your standard operating procedure.
Enforce Mandatory Multi Factor Authentication
Next up, make Multi Factor Authentication (MFA) non-negotiable for your entire organization. A password by itself is a broken lock. Forcing everyone to use MFA is one of the single most effective things you can do to stop an attacker, even if they’ve already stolen a user's password.
You can easily require MFA for all users in both AWS IAM and Azure Active Directory. Think of it as a powerful, easy-to-install barrier against common attacks like phishing. Don't treat MFA as an optional extra; it’s a baseline security requirement for every single person.
Establish Regular Permission Audits
Permissions aren't something you can "set and forget." A huge part of solid cloud identity management is running regular permission audits. You should schedule these reviews quarterly or semi-annually to fight "permission creep", the slow, silent accumulation of unnecessary access rights over time.
Your audits should zero in on a few key things:
- Find over-privileged accounts: Hunt down users or roles that have way more power than their job requires.
- Remove orphaned access: Make sure accounts for former employees or old services are shut down completely and immediately.
- Validate role definitions: Check if your RBAC roles still make sense for current job responsibilities.
By making audits a routine, you move from a reactive "firefighting" mode to a proactive security stance. This continuous check-up keeps your defenses strong as your team and infrastructure change, plugging security holes before they can be exploited.
Integrate Security with Cost Savings
A smart cloud identity strategy does more than just improve security. It can directly save you money. By using Role Based Access Control (RBAC) to delegate specific, non-security tasks, you can unlock some serious financial governance benefits.
For example, you could give a project manager an RBAC role that only lets them control the on/off schedules for their team's development servers. This tightens security by restricting their access, but it also empowers them to stop resource waste. When they turn off idle servers, they're actively cutting your cloud bill. It's a true win-win for your security and your bottom line.
How to Measure and Improve Your IAM Strategy
Getting your cloud identity management strategy off the ground is one thing, but it's not a set-it-and-forget-it project. The real work comes from continuous measurement and refinement. To justify your security efforts and figure out where to focus next, you need to be able to track what actually matters.
This is where you move beyond just setup and into a real cycle of improvement. By monitoring key performance indicators (KPIs), you turn abstract security goals into concrete, measurable results. These numbers give you a clear window into the health of your IAM program, helping you find weaknesses before they turn into full-blown vulnerabilities.
Key Metrics for Your IAM Dashboard
To get a real sense of how your strategy is performing, you need to focus on metrics that directly tie back to your security posture and day-to-day operations. These numbers tell a story about how well your identity controls are holding up in the real world.
- Time to Revoke Access: How fast can you cut off access for an employee who has left the company? A low number here is critical, ideally under an hour, to prevent orphaned accounts from becoming a security hole.
- Number of Privileged Accounts: Keep a running count of all your administrator or root-level accounts. If this number is high or keeps climbing, it's a major red flag that you're likely violating the Principle of Least Privilege.
- Failed Login Attempt Rate: A sudden spike in failed logins is often the first sign of a brute-force attack. Watching this trend helps you spot and react to threats as they happen, not after the fact.
A strong identity and access management program isn’t just about defense. It’s also about enabling the business to move quickly and safely. Consistently tracking these KPIs allows you to prove the ROI of your security investments.
Overcoming Common Roadblocks
Even the most well-thought-out strategy is going to hit a few bumps in the road. You might see pushback from users who find new security steps annoying, or frustration with roles that are just too complicated to be practical. For instance, developers might fight you on MFA if they feel it’s slowing down their coding workflow.
The solution is usually a combination of good communication and better tools. Take the time to explain why a control like MFA is so important, but also do everything you can to make the user experience as painless as possible. If your access roles are too complex, that’s a sign they need to be simplified to match how people actually do their jobs.
By getting ahead of these roadblocks, you ensure your cloud identity management strategy stays effective and adapts as your organization grows.
Frequently Asked Questions About Cloud Identity Management
Jumping into cloud identity management can bring up a lot of practical questions. Whether you're starting from scratch or just trying to tighten up your existing setup, you need clear answers to build a strategy that actually works.
Here are a few of the most common questions we hear from teams just like yours.
How Quickly Can We See Cost Savings from Better IAM?
Surprisingly fast. A smart cloud identity management policy can start trimming your bill in the very first billing cycle. The key is using Role-Based Access Control (RBAC) to manage when your resources are running.
When you stop idle servers from running overnight and on weekends, the savings are immediate. For example, just scheduling your development servers to power down outside of business hours can slash their running costs by as much as 70%. It’s a simple way to tie your security rules directly to your budget.
What Is the Difference Between IAM and CIAM?
While they sound similar, they serve very different groups.
Identity and Access Management (IAM) is all about your internal team: employees, contractors, and developers. Its main job is to lock down company resources and make sure internal security rules are followed.
Customer Identity and Access Management (CIAM), on the other hand, is built for your external users, like customers or partners. With CIAM, the priority shifts to a smooth user experience, easy sign-ups, and the ability to scale up to potentially millions of users, all while maintaining solid security.
Is It Hard to Get Started with Cloud Identity Management?
It's more approachable than you might think. You don't have to boil the ocean and overhaul everything at once. A great first step is to focus on a single, high-impact area, like enforcing Multi-Factor Authentication (MFA) for every single user. It's a quick win that dramatically improves security.
Another practical starting point is a simple access review. Go through your user lists, find and remove any "orphaned" accounts from former employees, and cut back any permissions that are obviously excessive. These small, targeted actions make a huge difference without turning into a massive project.
By tackling these foundational pieces first, you build momentum. From there, you can progressively add more sophisticated controls like automated lifecycle management and fine-grained policy enforcement. Taking it one step at a time makes building a strong cloud identity management framework feel manageable and effective.
Take control of your cloud costs without compromising on security. CLOUD TOGGLE makes it easy to schedule your AWS and Azure resources, use RBAC for safe delegation, and see immediate savings. Start your free trial today.